How to configure mailbox access using MS Graph application-only connection¶

Note
The privacy and security of any data access and handling associated with RG Email Sidebar deployment are guaranteed by the applicable Revenue Grid policies.
Introduction¶
This guide explains how to set up mailbox access for RG Email Sidebar and Sync Engine using the application-only connection type for Microsoft Graph. This method enables the app to securely connect to Microsoft 365 resources without relying on individual user credentials.
The MS Graph app-only connection type is ideal for organizations requiring access to more than just email, calendars, and contacts, such as files in OneDrive or collaboration tools in Teams. If your needs are limited to Exchange-specific functionality, consider configuring EWS app-only access.
This guide is for administrators setting up the mailbox connection for RG solution for the first time. For migration steps, refer to Migration from EWS delegated to Microsoft Graph application-only access.
Prerequisites¶
Before configuring mailbox connectivity using MS Graph app-only connection type, ensure the following:
- Microsoft Entra admin access: You need administrative rights to the Microsoft Entra admin center (formerly Azure AD portal) to register and grant permissions for the RG application.
- RG Admin Panel access: You must have platform administrator or profile administrator rights to complete the configuration.
Configuration¶
To configure RG Email Sidebar and Sync Engine to access your corporate Microsoft 365 mail server via an MS Graph app-only connection:
- Create an RG profile.
- Set the profile’s mailbox access type.
- Provision users to the profile.
- Verify connectivity.
- (Optional) Limit the RG app access to specific users.
Create RG profile¶
-
Log in to the RGES Admin Panel using your admin credentials.
-
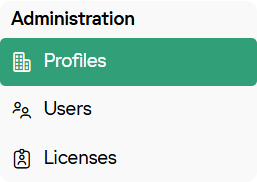
Go to the Profiles tab.
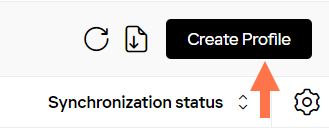
- In the upper-right corner, click Create Profile.
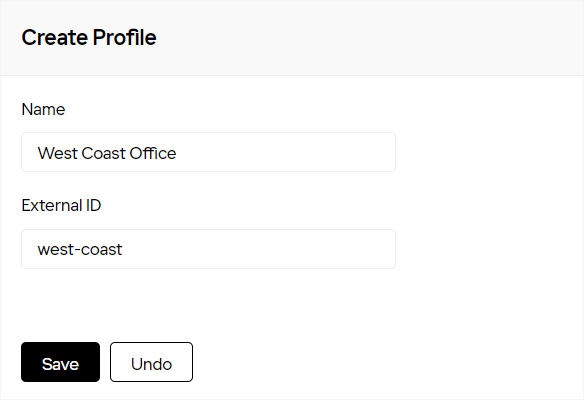
- Enter the Name and External ID, then click Save.
Important
Once saved, the External ID becomes read-only and cannot be changed.
A notification will confirm that the profile has been created successfully, and the profile details page will open.
Set profile’s mailbox access type¶
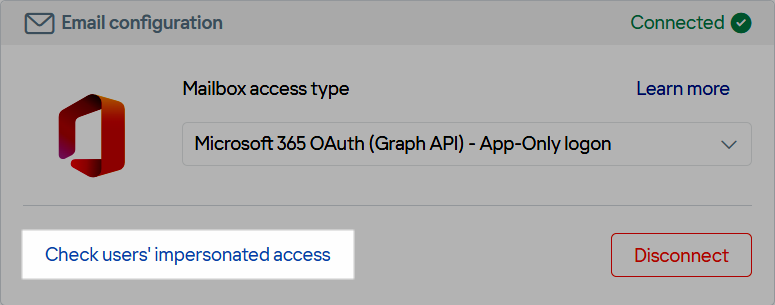
- In the profile, go to the Connectivity subtab.
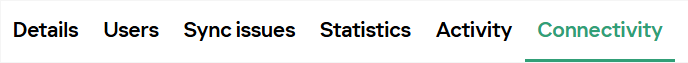
- In the Email configuration widget, in the Mailbox access type menu, select Microsoft 365 OAuth (Graph API) - App-Only logon.
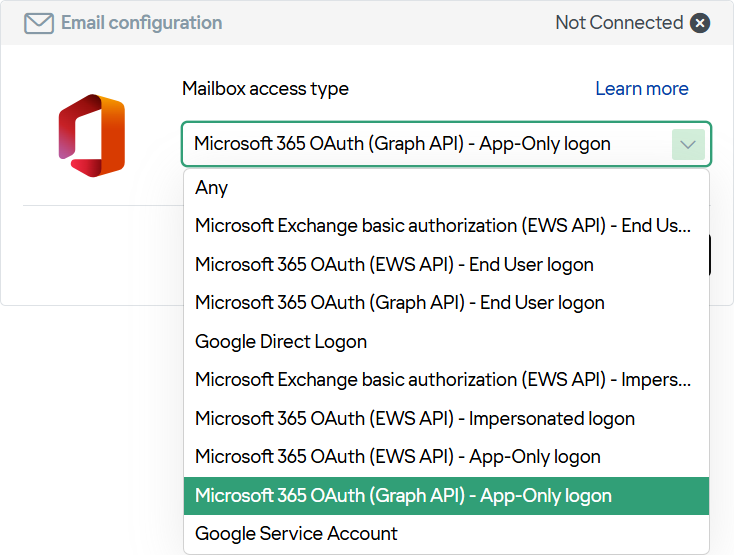
- Click Connect account. This will open the Microsoft 365 OAuth dialogue.
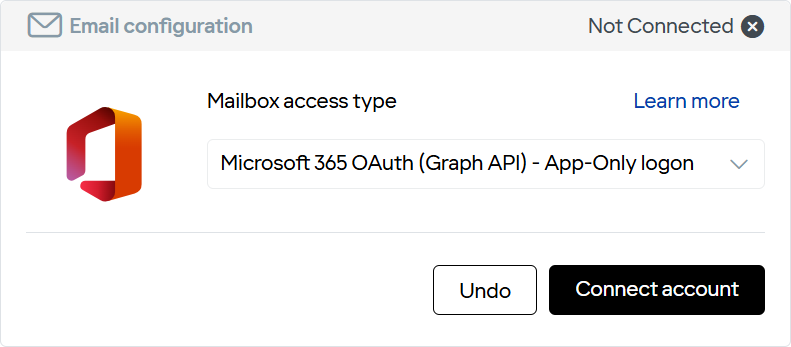
- Enter the Microsoft 365 admin credentials in the dialogue. These credentials are used only to grant permissions for MS Graph app-only access.
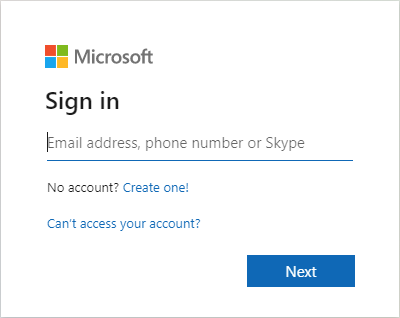
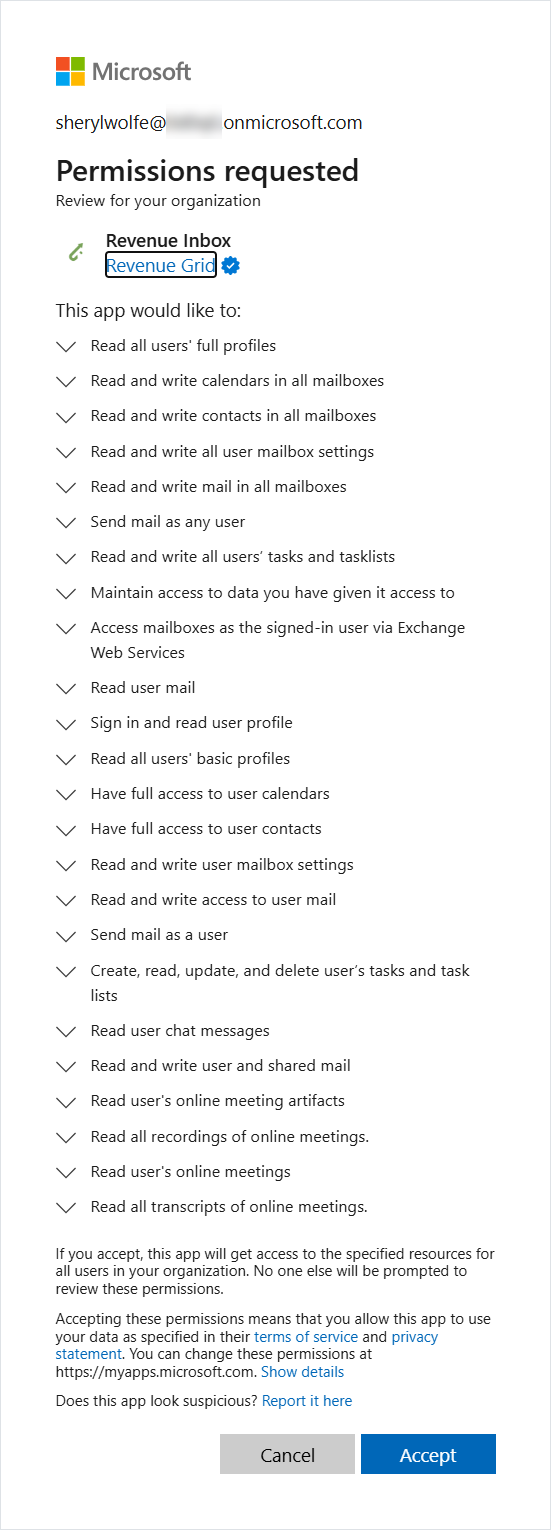
- In the permission authorization dialog, click Accept to grant the necessary permissions. If the connection is successful, the Email configuration section will display Connected.
Note
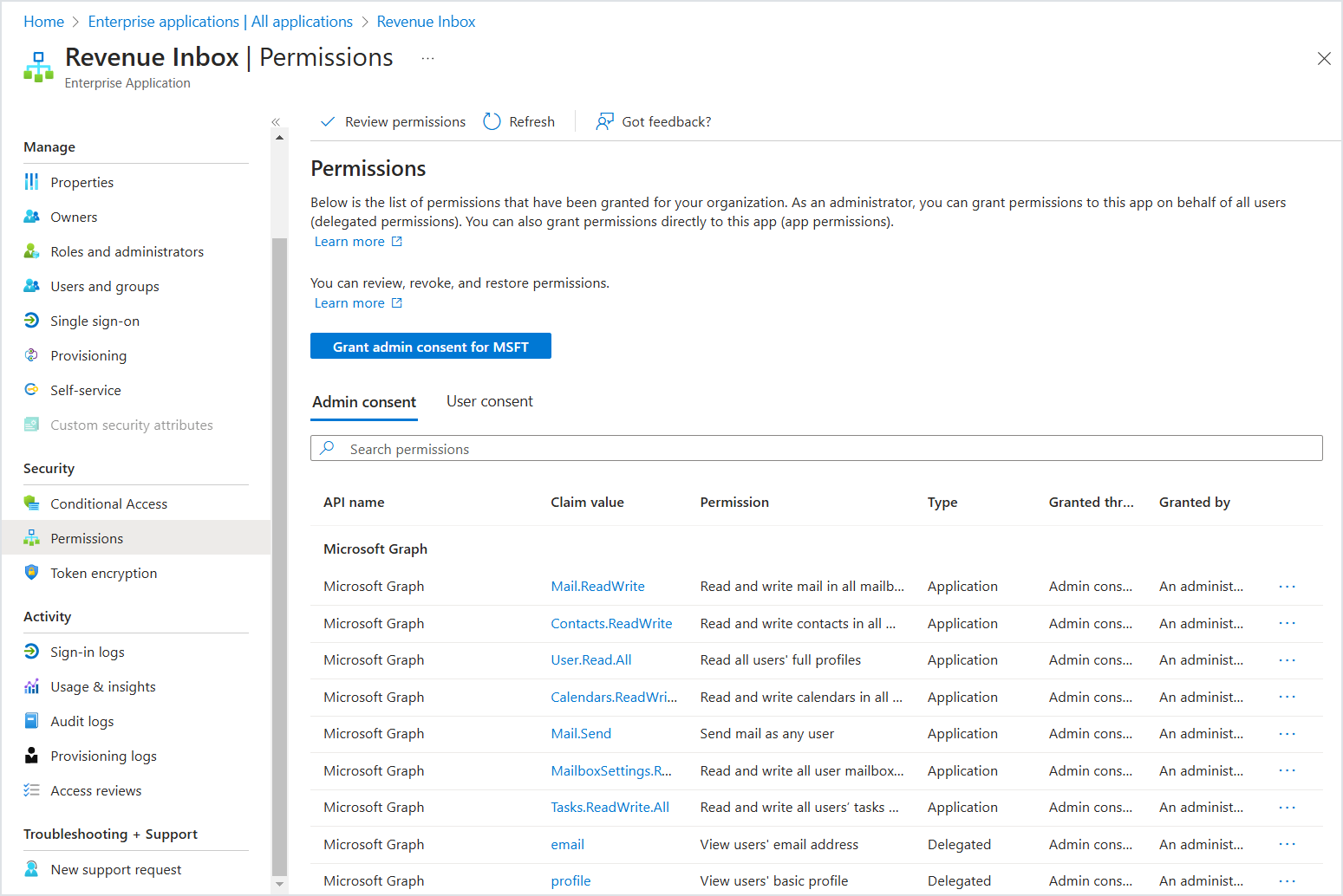
When permissions are granted, the Revenue Grid application is automatically registered in your Microsoft 365 tenant. If needed, you can revoke specific permissions in the Microsoft Entra admin center.
For example, RG requests the following permissions, among others:
- Chat.Read.All
- OnlineMeetings.Read.All
- OnlineMeetingTranscript.Read.All
- OnlineMeetingArtifact.Read.All
These permissions are required only if you plan to implement Revenue Grid Action Platform. If you don’t plan to integrate it, you can revoke these permissions without losing the functionality of the RG Email Sidebar and Sync Engine.
For detailed instructions on granting tenant-wide permissions, see Grant tenant-wide admin consent to an application.
Provision users¶
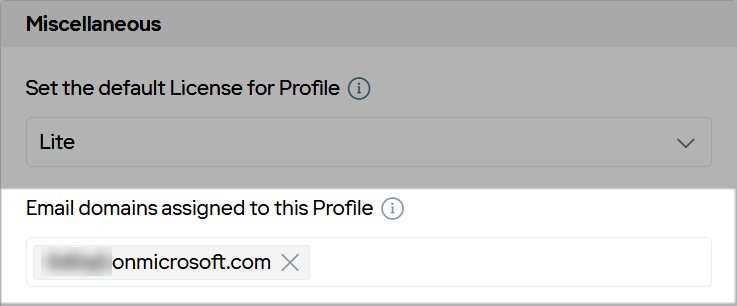
- In the profile, go back to the Details subtab.

- In the Miscellaneous section, in the Email domains assigned to this Profile field, specify the users’ email domains.
- Copy the Provisioning URL and share it with end users.
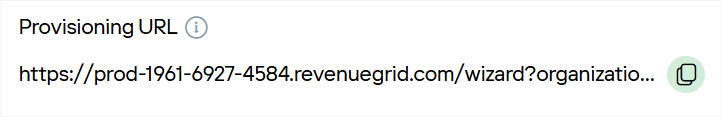
- Users should follow the Registration Wizard to complete registration.
If users’ email domains match those specified in the Email domains assigned to this Profile field, they will be automatically assigned to the profile.
Verify connectivity¶
Important
Be sure to complete this step. It is essential to finalize mailbox access configuration and ensure RG Email Sidebar and Sync Engine can access and sync users’ mailbox data.
- In the profile, open the Connectivity subtab.
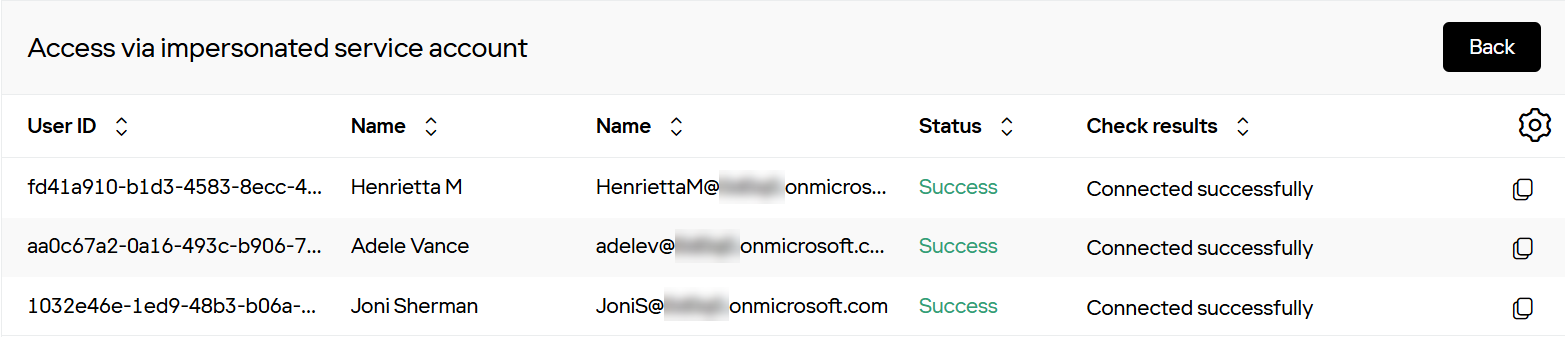
- In the Email configuration section, click Check users’ impersonated access.
Once verified, all user accounts assigned to the profile are configured to use MS Graph app-only access. Connection statuses will be displayed for each user.
(Optional) Limit RG app access to specific users¶
In many configurations, RG Email Sidebar (RGES) mailbox data access granted through app-only permissions must be restricted to a specific group of authorized users. This can be achieved using blacklist and whitelist settings via an application access policy.
To configure an application access policy and limit the scope of app permissions, follow these steps based on Microsoft’s guidance:
- Connect to Exchange Online PowerShell.
- Follow the instructions in Connect to Exchange Online PowerShell to establish a connection.
- Identify the app’s client ID and a mail-enabled security group.
- Find the app’s application (client) ID in the Azure app registration portal.
- Create a new mail-enabled security group or use an existing one, and note the group’s email address.
- Create an application access policy.
- Run the following PowerShell command, replacing AppId, PolicyScopeGroupId, and Description with the relevant details:
New-ApplicationAccessPolicy -AppId e7e4dbfc-046f-4074-9b3b-2ae8f144f59b -PolicyScopeGroupId [email protected] -AccessRight RestrictAccess -Description "Restrict this app to members of distribution group EvenUsers."
- Test the application access policy.
- Use the following command to verify whether the policy is applied correctly, replacing Identity and AppId with the appropriate values:
Test-ApplicationAccessPolicy -Identity [email protected] -AppId e7e4dbfc-046-4074-9b3b-2ae8f144f59b
The output will indicate whether the app can access the specified user’s mailbox.
Note
- Changes to application access policies can take up to 30 minutes to propagate in Microsoft Graph REST API calls.
- Always validate the results to ensure the policy is restricting access as intended.
Troubleshooting¶
If mailbox authentication issues occur, ensure the connectivity verification step is completed. Follow the steps in the corresponding instructions.
If issues persist, contact our support team.
See also¶
- Understanding application-only access
- Authentication differences between Exchange Web Services (EWS) and Microsoft Graph
- Migration from EWS delegated to Microsoft Graph application-only access
- How to configure mailbox access using EWS application-only connection type